Companies are increasingly reliant on technology for different aspects of their operations. IT has indeed come a long way and is now instrumental in the growth of many businesses, but it is still far from perfect. The more technology evolves, the more unwanted issues can arise with its use or misuse. So, how will you know these IT red flags if you do not have professional IT training?
As a non-technical person, you might not have the skills to address IT red flags, but you could identify common IT industry warning signs if you knew what they were. By knowing these signs and being extra vigilant, businesses can nip the problem in the bud through early mediation and avoid further issues that are detrimental to business operations. Here are the top five IT industry warning signs businesses should watch out for.
IT Red Flags: Increased Downtime
System downtime can result from a variety of events, some of which cannot always be avoided, like human error or natural disasters. However, if the downtime becomes more frequent or prolonged, this is likely due to IT red flag issues such as operating system bugs, network vulnerabilities, obsolete hardware, and so on.
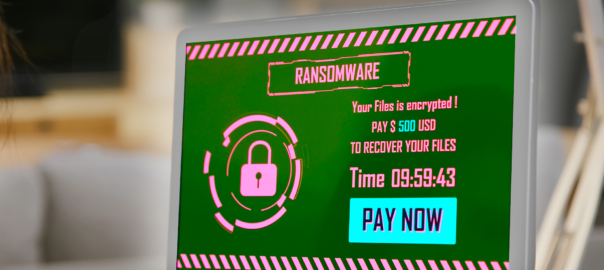
IT Red Flags: Security Breaches
If a hacker can penetrate your company’s cybersecurity system, it’s a sure indicator of IT trouble. A strong defense now will not remain a strong defense forever. You need to regularly upgrade and update your system to keep up with constantly evolving hacker techniques.
Sluggish Performance
Slow response times and lagging applications may have been commonplace in the 1990s, but it’s now 2024, so these issues can diminish user experience and productivity. When a computer becomes sluggish, there are many reasons, like insufficient memory, outdated hardware, malware infection, or other IT-related red flag matters.
Escalating Costs
Spending on IT makes sense if the expenses result in tangible results. But if the costs keep rising without notable changes in your IT system, then this is a sign of a problem. It might be time to audit your tech team and maybe even switch to a more efficient IT provider.
IT Red Flags: Lack of Scalability
Technology changes rapidly, and businesses should be able to adapt accordingly to keep up with the times and the competition. An inflexible IT solution will prevent you from doing this, limiting your growth potential.
The Best Way to Address IT Challenges in Your Company
Most, if not all, IT industry red flag signs mentioned above can be quickly resolved, or even avoided altogether, if your company has a reliable technical team to count on to take care of your systems. This is why you must choose your IT provider diligently. But how do you know you are making the right choice? Simple—your provider must fulfill all the 7 Components of Auditing an IT Provider.
Download a copy of the list here and find out exactly what kind of IT provider you need to hire. Make your selection wisely, and you will not have to deal with any kind of IT red flags. Instead, you can dedicate your attention to running and growing your business. If you want to learn more about IT management, just let us know, and we will be happy to set you up for a free consultation!